The React Native ecosystem just received a major wake-up call with the discovery of CVE-2025-11953, aptly dubbed “Metro4Shell.” This high-impact vulnerability targets the Metro bundler—the very heart of the React Native development workflow—transforming a seemingly simple path traversal flaw into a full-blown Remote Code Execution (RCE) vector. For any developer or security engineer working with JavaScript and mobile frameworks, this is a research piece you cannot afford to ignore.
The Anatomy of the Flaw
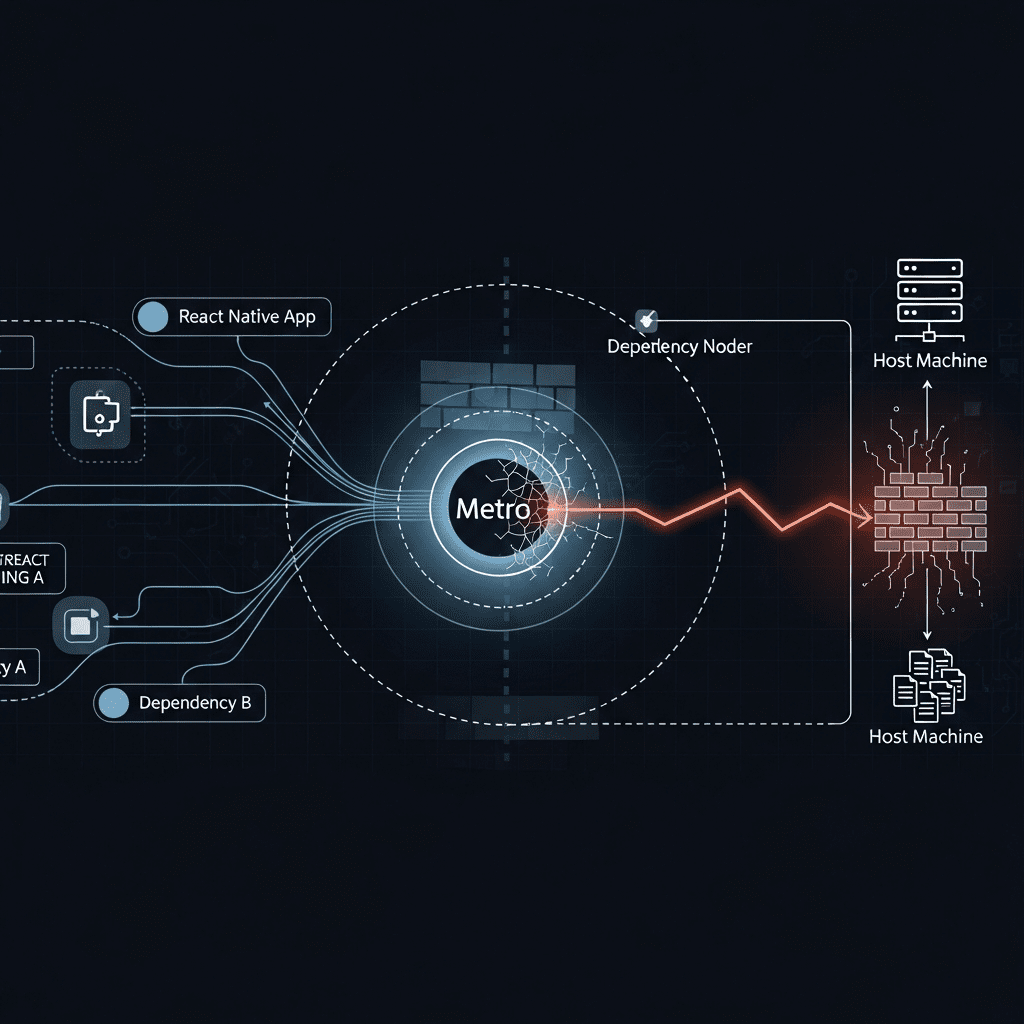
Metro is the JavaScript bundler for React Native, responsible for resolving dependencies and serving the compiled bundle to the mobile app during development. The Metro4Shell vulnerability exploits an oversight in how the bundler handles incoming file requests. By utilizing a path traversal technique, an attacker can bypass the intended directory restrictions and access sensitive files on the host machine.
While path traversal is a classic vulnerability, the escalation to RCE is what makes CVE-2025-11953 particularly dangerous. In a typical development environment, an attacker could potentially trick a developer’s local Metro server into executing malicious scripts, effectively seizing control of the workstation used for mobile app development.
Why Metro4Shell is a Game-Changer
The impact of this vulnerability is significant due to the ubiquitous nature of the Metro bundler in the React Native world. Here are the primary reasons why this research is sending ripples through the community:
- Supply Chain Risk: Developer workstations are high-value targets. Compromising a developer’s machine can lead to the injection of malicious code into legitimate enterprise applications.
- Trust Boundary Erosion: Developers often treat their local dev servers as “safe” zones. Metro4Shell proves that internal development tools require the same rigorous security auditing as production-facing APIs.
- Ease of Exploitation: Path traversal vulnerabilities are notoriously reliable to exploit once the specific endpoint and normalization bypass are identified.
Technical Impact and Mitigation
The research highlights that the vulnerability stems from insufficient validation of user-supplied paths. Because the Metro bundler is often left running in the background during long development sessions, it provides a persistent attack surface. If an attacker can reach the developer’s network or trick them into visiting a malicious site that makes cross-origin requests to localhost, the results can be catastrophic.
To secure your environment, it is imperative to follow these steps:
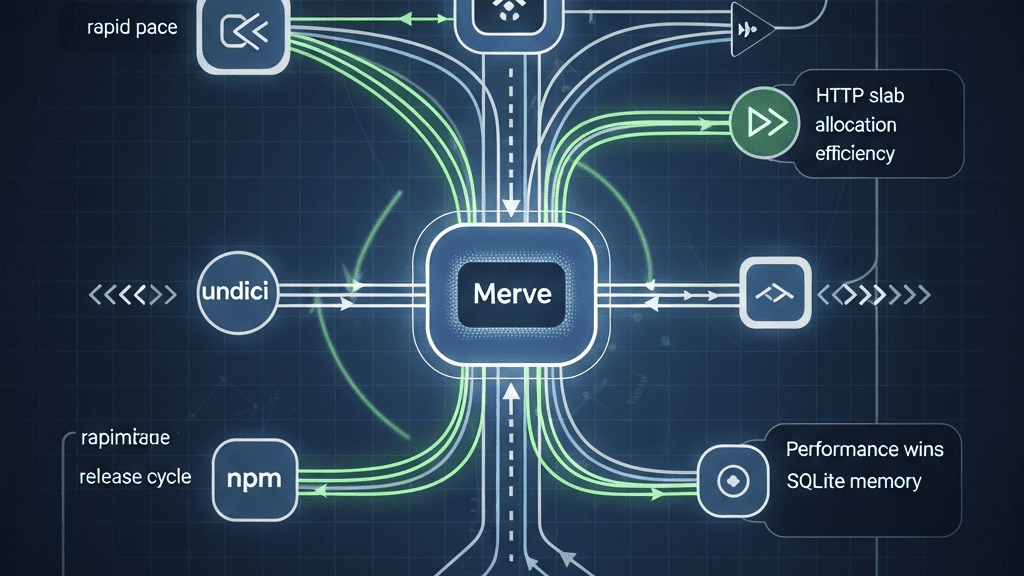
- Update Immediately: Ensure your project is using the latest patched versions of Metro and React Native.
- Network Isolation: Avoid running development servers on public or untrusted networks without proper firewall configurations.
- Audit Dependencies: Regularly use tools like
npm auditoryarn auditto identify vulnerable packages within your dependency tree.
The Bottom Line
CVE-2025-11953 is a stark reminder that our development toolchains are just as critical as our production code. The Metro4Shell disclosure is an incredible piece of technical research that underscores the need for constant vigilance in the Node.js and React Native ecosystems. Stay updated, stay curious, and most importantly, keep your dev environment locked down!
Source: Read the full article here.