The Node.js community has just dropped a critical coordinated security update, and if you’re running production workloads, it’s time to get excited about these patches! This release targets all active release lines—25.x, 24.x, 22.x, and 20.x—bringing essential hardening to the core runtime. While we aren’t seeing new features today, the technical precision of these fixes ensures that our applications remain resilient against sophisticated memory and permission-based exploits.
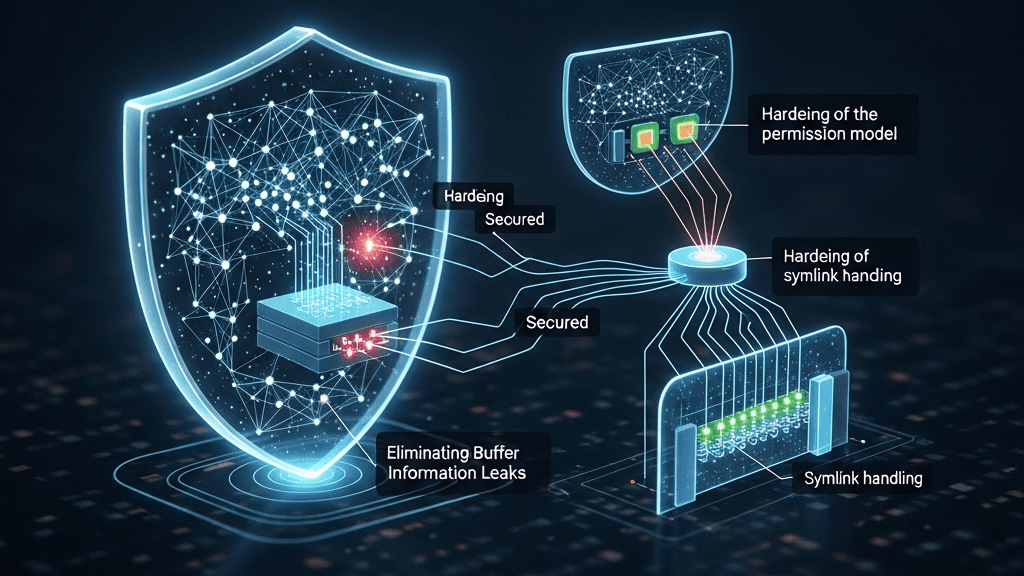
Eliminating Buffer Information Leaks (CVE-2025-55131)
One of the most significant fixes in this cycle addresses a High-severity race condition in buffer allocation (CVE-2025-55131). In high-performance runtimes, memory management is a balancing act. Previously, certain optimizations in Node.js could defer memory zero-initialization. Under specific conditions—such as high concurrency or execution within a vm context using a timeout—a buffer could theoretically be exposed to userland before it was fully wiped.
The risk? Residual data from previous allocations (which might include sensitive in-process secrets like API keys or user tokens) could be leaked through Buffer.alloc() or TypedArray constructors. The January update solves this by enforcing strict memory initialization before any buffer is surfaced to the application. By decoupling allocation from exposure, Node.js restores deterministic safety to memory handling, even under heavy load or execution interruptions.
Hardening the Permission Model (CVE-2025-55130)
The experimental Node.js Permission Model continues to evolve into a powerhouse feature for secure-by-default applications. This release addresses a High-severity vulnerability (CVE-2025-55130) involving symlink handling. In complex file systems, symlinks can sometimes be leveraged to bypass path-based restrictions. This update tightens how the runtime resolves and validates symlink paths, ensuring that your security boundaries remain uncompromised regardless of how the underlying file system is structured.
Are You Impacted?
While all production environments should prioritize these updates, you are at a higher risk if your application fits any of the following criteria:
- High-Concurrency Environments: Applications handling thousands of simultaneous requests where memory allocation patterns are highly dynamic.
- Multi-tenant Execution: Systems using the
vmmodule with timeouts to run untrusted or isolated code. - Direct Buffer Exposure: APIs that return raw buffer data or serialized memory objects directly to clients or logging systems.
- Permission-Restricted Runtimes: Environments relying on the
--experimental-permissionflag to restrict file system access.
The Expert Verdict: Patch Now
This release is a masterclass in why coordinated vulnerability disclosure is vital for the ecosystem. The fixes span memory safety, protocol processing, and resource management—areas that form the bedrock of a stable production environment. Don’t wait for a scan to flag these issues; update your containers and server environments to the latest patched versions of Node.js 20, 22, 24, or 25 today to ensure your infrastructure remains a fortress.
Source: Read the full article here.